
“30% to 40% of cyber incidents in Africa go publicly undocumented” – Interpol
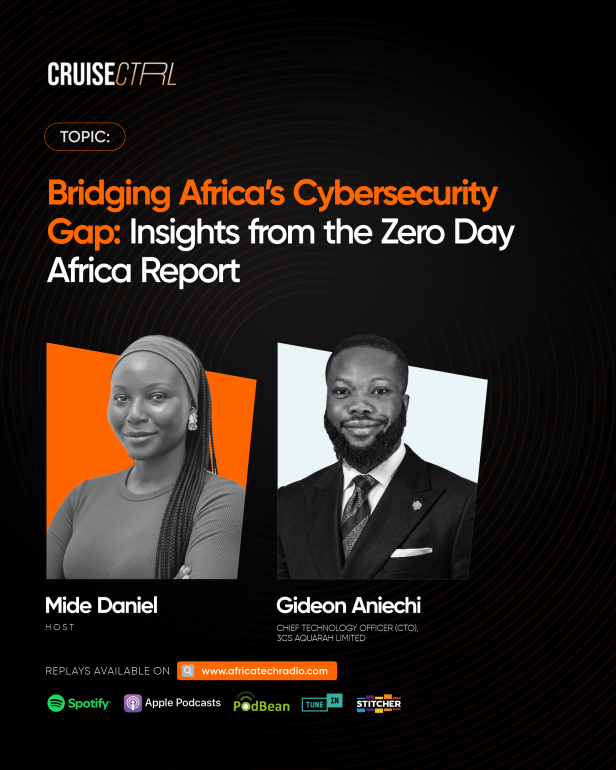
Africa finds itself at a critical crossroad between economic acceleration and unprecedented cyber risk. In a recent interview on Africa Tech Radio, Gideon Aniechi, Chief Technology Officer at 3Cs Aquarah Limited, announced the launch of the Zero Day Africa Report, which will support cybersecurity leaders across Africa with insights into cyber incidents and how they impact the continent.
The Zero Day Africa Report, launched by 3Cs Aquarah on April 10, 2026, focuses on strategic intelligence for cybersecurity leaders across Africa required to secure the continent’s future.
The reality is sobering: according to Interpol, between 30% and 40% of cyber incidents in Africa remain publicly undocumented. Zero Day Africa changes the narrative by providing a structured, African-centric analysis that doesn’t just announce breaches but breaks down the “how,” the “why,” and the real-world consequences for organizations—from financial hemorrhage to regulatory fallout.

Here are the four key pillars from Gideon’s interview on Africa Tech Radio, optimized for today’s cybersecurity leaders.
1. Why Situational Awareness is the New Firewall
The Zero Day Africa Report serves as a vital mirror for the continent’s tech ecosystem, moving beyond simple incident reporting to provide deep, structured analysis. Gideon Aniechi emphasized that Africa’s digital footprint — driven by fintech, mobile banking, and cloud migration — is expanding, just as much as the attack surface.
The report’s primary value lies in its ability to translate “how” attacks occur into actionable insights for executive stakeholders. The report moves beyond simply announcing breaches; it interrogates the “how,” “why,” and the real-world consequences, such as regulatory risks and service disruptions, to give technical teams a localized map of the battlefield.
2. Cloud Misconfigurations and Insider Threats are the Silent Killers of Digital Trust
One of the most sobering insights from the interview was the identification of recurring patterns in security gaps. Aniechi highlighted that cloud misconfigurations and third-party exposure remain the “low-hanging fruit” for cybercriminals across Africa.
Some highlighted examples of this recurring weakness are listed below (the failure to patch known vulnerabilities):
● The South Africa Example: A major pharmacy was exposed to a vulnerability that had a patch available for five years before the breach occurred.
● The Senegal Breach: A massive data loss involving the national visa system was traced back to an unpatched VPN and exposed privileged credentials.
● The Cloud Trap: Organizations are migrating to the cloud but “relocating” their existing on-premise vulnerabilities rather than fixing them, leading to massive financial losses—such as a startup losing $28,000 in API tokens within days due to poor security architecture.

Furthermore, the report documents the rising complexity of insider threats and the exploitation of exposed systems within sectors like banking and telecommunications.
Aniechi noted that the real-world consequence of these breaches isn’t just financial loss; it is the erosion of trust, which is the most expensive currency to lose in a developing digital economy. He noted that proactive measures, such as strengthening identity controls and reducing third-party reliance, are now non-negotiable for institutional survival.
3. Building Cyber Resilience in Africa: Shifting from Defense to Predictive Strategy
The final pillar of the Zero Day Africa framework is a shift in mindset: moving from “hoping to stay safe” to building for resilience. Gideon Aniechi urged technical teams to prioritize incident response readiness and continuous monitoring as core business functions.
By analyzing the real-world consequences detailed in the report—including regulatory risks and service disruptions—organizations can make better, data-backed decisions. As Africa continues its tech ascent, the Zero Day Africa Report by 3Cs Aquarah stands as the credible platform organizations need to bridge the cybersecurity gap and ensure that their digital foundations are as secure as they are innovative.
4. Cybersecurity as Governance: A Roadmap for the Non-Technical CEO
One of the core missions of the Zero Day Africa Report is to move cybersecurity out of the “IT basement” and into the boardroom. Aniechi argues that trust erosion is far harder to recover from than financial loss.
With the rise of insider threats, where employees with deep access become the primary attack vector, security must be treated as a strategic imperative. The report is designed specifically for both technical and non-technical leaders. It also provides a “to-do list” for CEOs to hold their technical staff accountable, shifting the focus from “Checkbox Compliance”—doing just enough to pass an audit—to “Security-Based” systems designed to survive an actual attack. In addition, the glossary section makes it particularly
easy for non-technical leaders to understand the terminology used across the document.
The Path Forward
The first 60 minutes of a cyber-attack do not define your organization; the months of preparation before the attack do. Aniechi emphasizes that a prepared organization is defined by its Business Continuity Plan (BCP) and Incident Response Plan (IRP), tested rigorously before the “day of reckoning.”
To stay ahead of the curve, you can download the Zero Day Africa Report directly from the 3Cs Aquarah website or subscribe to their bi-weekly LinkedIn newsletter for real-time situational awareness across the continent.

Powerful Quotes from the Interview
1. On Visibility: “Zero Day Africa was born from the need to provide visibility… We wanted to ensure we give the African audience visibility into our own data, in our own language.”
2. On Growth vs. Security: “We are racing ahead with visibility, and maturity is trying to catch up with us.”
3. On Basic Failures: “The single most recurring weakness is failure to patch known vulnerabilities, combined with poor credential and network hygiene.”
4. On Compliance: “The report calls this ‘checkbox compliance’—where you just want to check the box… Organizations keep repeating the same basic mistakes instead of moving to zero trust principles.”
5. On Trust: “Financial losses will always happen… but the one that is most prevalent and even more difficult to come out from is a long-term trust erosion.”
6. On Insider Threats: “If death inside cannot kill you, it’s difficult for something outside to penetrate.”
7. On the Cloud: “Securing your cloud infrastructure is more than just migrating… You are not just moving; you are often exposing yourself more or increasing your attack surface.”
8. On CEO Responsibility: “Cybersecurity is no longer a technical function; it is now a governance responsibility.”
9. On Preparation: “What separates a prepared organization from a vulnerable one is not what you do on that day; it is what you have done before that day.”
10. On the African Mindset: “African security is compliance-based, not security-based. We have to switch that narrative.”








Post comments (0)